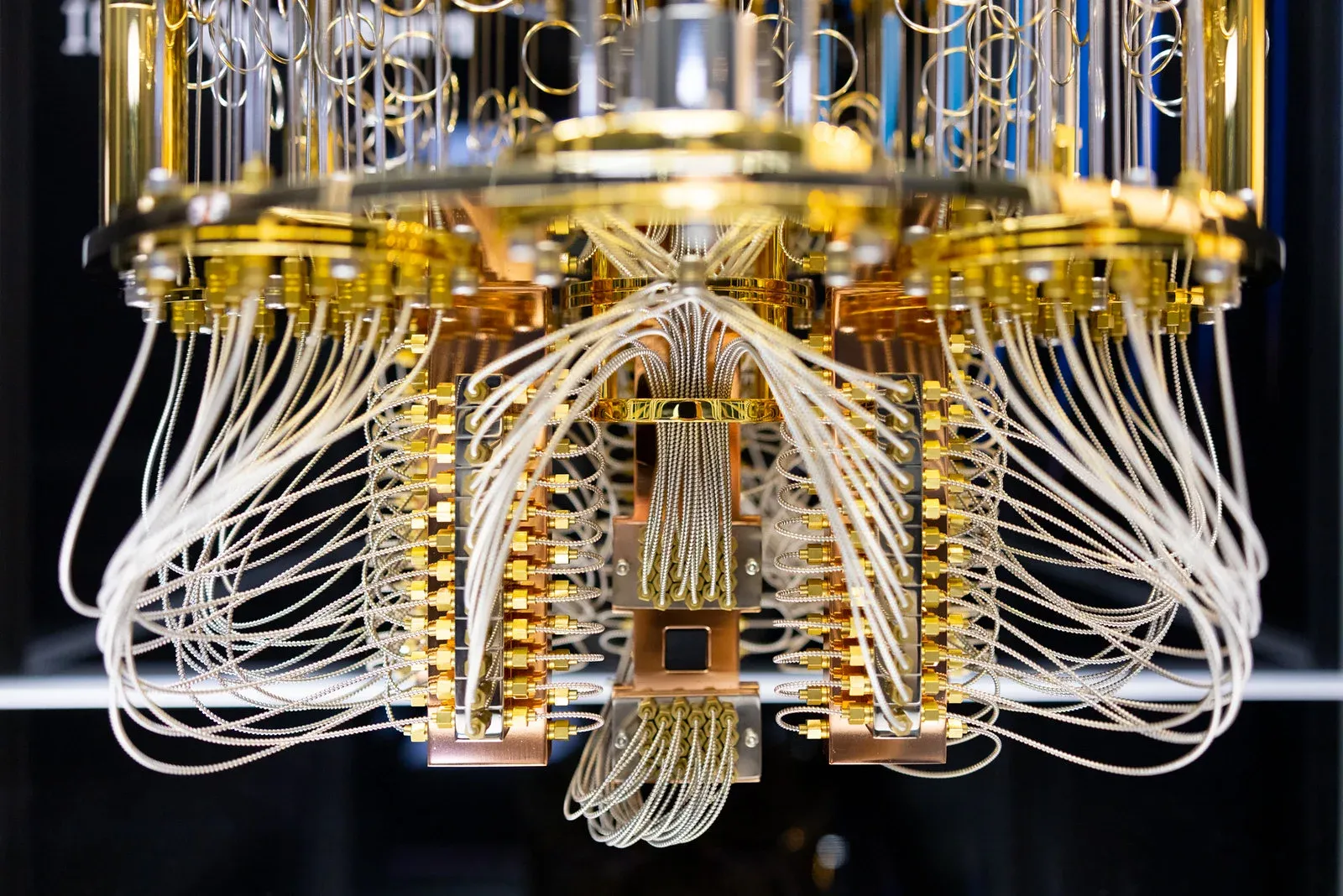
A classic hacking technique known as "rowhammer" has been adapted to exploit vulnerabilities in certain quantum computers, specifically those that are noisy and error-prone.
This development underscores that even advanced quantum systems are not immune to traditional cyber threats.
Rowhammer Meets Quantum
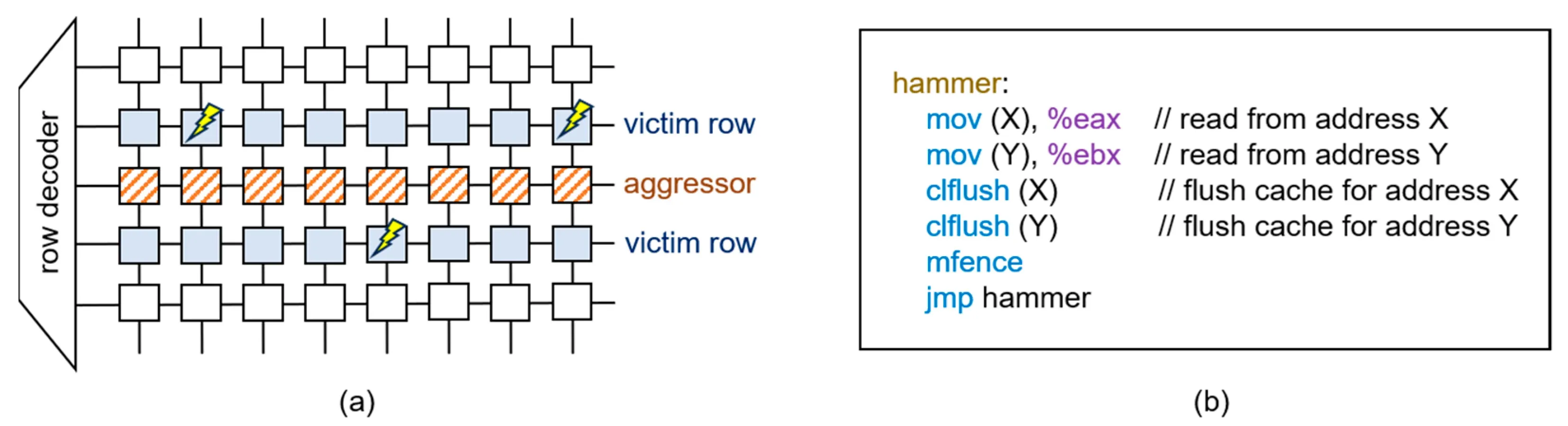
Originally, the rowhammer attack targeted classical computer memory by repeatedly accessing specific memory rows to induce bit flips in adjacent rows, leading to potential data corruption or unauthorized access.
Recent research indicates that similar strategies can be employed against quantum computers, particularly those with high error rates.
By introducing controlled disturbances, attackers can manipulate qubits, the fundamental units of quantum information, potentially compromising the system's integrity.
Implications for Quantum Computing Security
This revelation challenges the perception of quantum computers as inherently secure due to their complex and novel architecture.
It highlights the necessity for robust error correction and security protocols tailored to quantum systems.
As quantum computing continues to evolve, integrating classical cybersecurity measures with quantum-specific safeguards will be crucial to protect against such hybrid threats.
Strengthening Defenses: The Path Forward
To mitigate these vulnerabilities, researchers and developers must prioritize the development of quantum error correction techniques and security frameworks that account for both quantum-specific and classical attack vectors.
This includes rigorous testing of quantum hardware for susceptibility to such attacks and implementing countermeasures that can detect and prevent unauthorized manipulations.